What does HIPAA stand for?
HIPAA stands for Health Insurance Portability and Accountability Act of 1996 and is United States legislation that provides data privacy and security provisions for safeguarding medical information.
Is Text Messaging HIPAA Compliant?
The simple answer is that text messaging is HIPAA-compliant under certain circumstances and provided that “administrative, physical and technical safeguards [exist] to ensure the confidentiality, integrity, and security of electronically stored or transmitted private health information.”
Learn More
How can Doctors Receive PHI and Still be in Compliance with HIPAA?
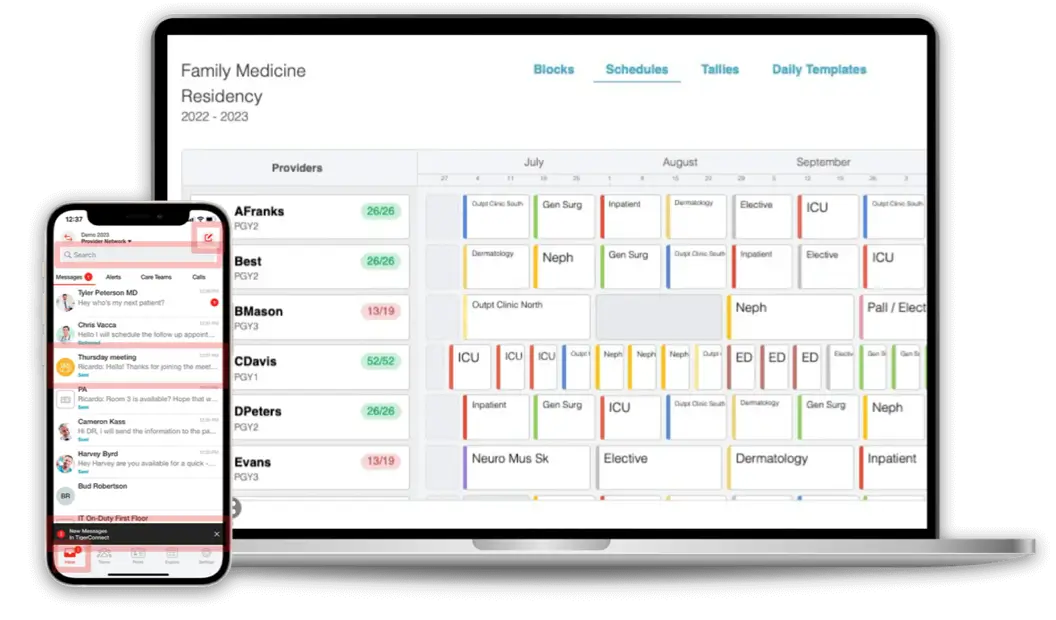
If doctors and other medical professionals were no longer allowed to communicate patient data on their mobile devices due to HIPAA and the Omnibus Rule, this would have had serious implications for the standard of healthcare received by patients; but fortunately the issues surrounding how doctors can receive ePHI in compliance with HIPAA can be resolved with a secure text messaging solution from TigerConnect.
Learn More
Does Text Messaging Violate HIPAA Guidelines?
The HIPAA guidelines for text messaging were introduced due to the increasing number of medical professionals who were using personal mobile devices (Smartphones, laptops, tablets etc.) to access electronic protected health information (ePHI) and communicate it – via text – to colleagues. TigerConnect has developed a secure text messaging platform which makes the question “Does text messaging violate HIPAA guidelines?” irrelevant. The platform enables the transmission of encrypted ePHI and viewing within a secure cloud-based platform; which authorized users can gain access to via an on-demand or web application.
Learn More
Why Was a HIPAA Texting Policy Needed?
The HIPAA texting policy introduced in the Final Omnibus Rule aims to eliminate the risk of patient health information being compromised during the sending or receiving of sensitive data via SMS, or while patient health information is kept on a portable mobile device (cell phone, tablet, Smartphone, etc.).
Learn More
Why Were HIPAA Encryption Requirements Established?
Due to technological advances and changes in work practices, sensitive patient health information is often communicated by portable mobile devices such as cell phones, Smartphones, and tablets. The potential for data being compromised when using public Wi-Fi or open cell phone networks is vast. The revised HIPAA data encryption regulations were created to address these issues.
Learn More
What Should I know about HIPAA Compliance for Clinical Texting?
Prior to the guidelines for HIPAA compliant clinical texting being introduced, it had been estimated by the Centre for Democracy and Technology that 66 percent of all breaches of PHI were attributable to the loss or theft of a personal mobile device. Due to technological advances and changing work practices, more than 80 percent of healthcare professionals now access PHI or communicate patient data via their mobile devices (according to a study by the Health Research Institute) – although not always within HIPAA compliance for clinical texting.
Learn More
What Should I know about HIPAA Compliance for Email?
According to the US Department of Health and Human Services website, the revised rules about HIPAA compliance when sending emails do not prohibit the use of emails when sending ePHI, and at first reading, the regulations regarding HIPAA compliance for email would suggest sending encrypted ePHI by email is acceptable – although it would be necessary for both the sender and the recipient to have the same encryption software.
Learn More
What Do The HIPAA Regulations for Email Actually Say?
According to the US Department of Health and Human Services website, “the [HIPAA] Security Rule does not expressly prohibit the use of email for sending e-PHI. However, the standards for access control, integrity and transmission security require covered entities to implement policies and procedures to restrict access to, protect the integrity of, and guard against unauthorized access to e-PHI.”
Learn More
Why Do We Need a HIPAA-Compliant Text Messaging Service?
The use of email and SMS to communicate sensitive patient information was effectively outlawed by HIPAA due to copies of messages stored by service providers, the inability to retract and delete sent messages and the risk of a communication being intercepted in an area of publicly-accessible Wi-Fi.
Learn More
What Is HIPAA Compliant Encryption for Text Messaging?
HIPAA-compliant encryption for text messaging is a security measure to guard against unauthorized access to ePHI transmitted over a communication network. Its purpose is to make any sensitive patient data that is compromised while in transit unusable, unreadable and indecipherable to any third party who accesses it.
Learn More
Who Do The HIPAA Regulations for SMS Apply to?
The changes to the HIPAA regulations for SMS messaging extended who must comply with the mandated best practices. In addition to medical professionals, health insurance providers (including employers), health insurance clearing houses (including fund managers), and any subcontractor, “associate,” or third-service provider who has access to PHI* is now also subject to the HIPAA regulations for texting.
Learn More
How Can We Make Smartphones HIPAA Compliant?
In order to make smartphones HIPAA compliant, the organization for which the Smartphone user is an employee, associate or third party service provider must implement a secure messaging solution which protects the integrity of ePHI when it is at rest and in transit. TigerConnect facilitates HIPAA-compliance with regard to most smartphones.
Learn More
What Are the Revised HIPAA Text Messaging Software Guidelines?
One of the most important revisions to the guidelines for HIPAA texting software was that the scope of the Health Information Technology for Economic and Clinical Health Act and Health Insurance Portability and Accountability Act was extended to include everybody who may have access to PHI or transmit sensitive patient data in text messages from their mobile devices (Smartphones, tablets and cell phones).
Learn More
Is Texting in Hospitals HIPAA Compliant?
The revised guidelines for “when is texting in hospitals HIPAA compliant” broadened the scope of the Act to include everybody who may have access to protected health information (PHI). The regulations regarding HIPAA compliant hospital texting now also apply to third party services providers such as administrators, fund managers and insurance brokers – and any subcontractors employed by them. These third parties must comply with the revised HIPAA regulations or risk being fined by the Office of Civil Rights should a breach of PHI occur.
Learn More
Why Do We Need a HIPAA Mobile Device Policy?
In order to guide authorized users on the most appropriate way to use the secure messaging app, healthcare organizations must develop policies to ensure compliance with HIPAA – these policies also apply to business associates and third party service providers for the healthcare organization.
Learn More
How Should We Text Laboratory Results and Be HIPAA Compliant?
In order to text lab results in compliance with HIPAA, lab technicians should log into a secure application where they can view ePHI they receive and upload any relevant additional information. A text message can then be sent to a medical professional containing the lab results as an image or pdf.
Learn More
What’s the Easy Path for HIPAA Compliant Texting for Our Hospital?
Despite the many, many pages in the Health Insurance Portability and Accountability Act (HIPAA) relating to the security of protected health information, it is not difficult to achieve HIPAA compliant texting for your hospital. All that is needed is a secure text messaging platform from TigerConnect and a system administrator to monitor usage of the text messaging platform.
Learn More
What’s the Best Solution for PHI and HIPAA Compliance for Text Messaging?
TigerConnect’s secure texting solution allows authorized personnel to access PHI through a secure closed network on most mobile devices or via the web. The secure texting system meets all the physical and technical requirements to safeguard the integrity of PHI and HIPAA compliance for text messaging, and automatically generates audit logs to assist administrators with their obligations under the administrative requirements.
Learn More
How to Choose a HIPAA Compliant Texting Vendor?
To help ease the difficulty of choosing a secure text messaging vendor, TigerConnect has compiled a white paper “The Top Ten Considerations when Selecting a Secure Text Messaging Solution” that provides advice on the most important considerations you should take into account when evaluating a secure text messaging solution and the vendor who is marketing it. Click below to find out how to get yours.
Learn More
What Is HIPAA-Compliant Texting for Physicians?
Using a secure texting platform, physicians can send text messages in compliance with HIPAA by composing the message within a secure platform, accessible from their desktop computers or mobile devices. The recipient receives a notification or a text containing a link to the encrypted message, allowing them to access the message after authenticating their identity with a unique username and password.
Learn More
What Are The HIPAA Rules for Email Encryption?
What HIPAA actually says about email encryption is that covered entities must “implement a mechanism to encrypt and decrypt electronic protected health information,” and most communication experts agree that healthcare organizations who want to facilitate the communication of protected health information by email should double their encryption protection, so that encrypted communications are sent over an encrypted connection “just to be on the safe side.”
Learn More
Why Were HIPAA Guidelines for Texting Needed?
HIPAA SMS guidelines were needed to eliminate the risk of patient health information being breached during the transmission or receipt of sensitive data, or while such data was maintained on a mobile device (cell phone, tablet, smartphone etc.). Research had shown that more than 80 percent of physicians use mobile devices to communicate with their patients or access patient health information, while a further study revealed that 66 percent of patient health information breaches were attributable to mobile devices being lost or stolen.
Learn More
What Are the HIPAA Messaging Compliance Rules?
The HIPAA messaging compliance rules concentrate on protecting patient privacy and how breaches – if they happen should be dealt with; but there are also other changes to the regulations within the Final Omnibus Rule that all individuals with responsibility for the integrity of patient health information should be aware of in the event that patient data stored on mobile devices is compromised.
Learn More
How to Share Files in Compliance with HIPAA?
Fortunately, TigerConnect’s secure messaging solution enables medical professionals to share files and collaborate securely without risking a breach of ePHI, and with the result that workflows are accelerated, efficiency is increased and patients have an enhanced healthcare experience.
Learn More
How Do I Choose a HIPAA Compliant Texting Product?
Among the many options available for communicating electronic protected health information in compliance with the Health Insurance Portability and Accountability Act (HIPAA), a HIPAA compliant texting product is the most favored, and least likely to result in a breach of ePHI. Follow the link below to learn more about the features and benefits of secure text messaging products and for further information about how a HIPAA compliant text product fulfills the physical, technical and administrative requirements of the HIPAA Security Rule, including a download for our “Top Ten Considerations when Selecting a Secure Text Messaging Solution” white paper.
Learn More
Is SMS HIPAA Compliant?
In order for an SMS to be HIPAA compliant, both the sender and the recipient should be authorized users of a secure messaging system which enables them to access and transmit ePHI as required. With a secure messaging platform, all messages are encrypted and do not have the security risks associated with standard messaging systems, aka SMS. The secure messaging system must be capable of removing users and remotely deleting messages sent within the application in case a personal mobile device is lost, replaced or stolen. The application must also provide system administrators with the ability to gather audit logs to adhere to best practices policy for HIPAA compliance and SMS.
Learn More
Is Sending Files HIPAA Compliant?
Once a platform for secure messaging (like TigerConnect) is implemented, healthcare organizations also have a responsibility to produce guidelines for authorized users to access and transmit ePHI. These guidelines should outline when it is appropriate to access ePHI and how it should be transmitted so that the sending of files is HIPAA compliant. Policies for how to send files in compliance with HIPAA are essential; for without them, every other precaution that a healthcare organization has taken to be in compliance with HIPAA could be ineffective, and the same penalties would apply when a breach of ePHI occurs.
Learn More
Who Do the Rules for Text Messages and HIPAA Compliance Apply to?
In addition to employer, health insurance providers, health insurance clearinghouses and medical professionals, the rules for text messages and HIPAA compliance now apply to associates, subcontractors or any third-party service provider who has access to PHI. This means that if an insurance provider wants details of the treatment a patient has received in hospital, it also has to be an authorized user on a secure messaging system in order to retrieve that information.
Learn More
How Can I Implement Secure Communications with HIPAA Email Compliance?
Facilities may begin with policies that prohibit electronic transmission such as a “no texting policy,” but this does not guarantee employees will stop using their own devices for work communication. Ultimately, the best answer is to implement a solution that will address electronic transmission and use this technology to optimize current workflow in the healthcare facility, like TigerConnect.
Learn More
What Makes a Texting Solution HIPAA Compliant?
A HIPAA texting solution complies with the legislation for the security of electronic protected health information (ePHI) by allowing authorized users access to encrypted data via a secure messaging platform. The texting solution is HIPAA compliant due to administrative controls which exist on the secure platform to retract or delete communications that may be in breach of HIPAA regulations, remotely wipe sensitive content from a mobile or desktop device, and remove a user from the network if – for example – their mobile device is lost or stolen.
Learn More
Is There a Guide to Secure Texting?
Yes. Secure texting best practices guidelines were introduced to reduce the risk of protected health information being compromised during the transmission or receipt of patient data, or while such data was stored on a portable or mobile device (cell phone, tablet, Smartphone etc.). Studies had shown that more than 80 percent of doctors use mobile devices to access protected health information and communicate with their patients, while further research revealed that 66 percent of reported breaches of patient data were due to mobile devices being lost or stolen.
Learn More
What Is HIPAA Compliant Messaging?
HIPAA compliant messaging is a means of secure communication by which healthcare organizations and other associated businesses can safeguard electronic protected health information (ePHI) while facilitating an open flow of sensitive patient information between authorized users. Platforms and apps for secure messaging meet healthcare industry standards to ensure the integrity of ePHI during the secure communication of sensitive patient information and provide a secure alternative to “traditional” text messaging.
Learn More
How Have The HIPAA Rules Regarding Text Messaging Benefitted Patients?
Case studies have shown that healthcare professionals have been able to treat patients quicker and more effectively through a secure messaging system than through any other mode of communication. The ability for secure messages to be transmitted across various devices and platforms has created a more efficient workflow – both in the hospital environment and in home health settings – which has resulted in healthcare professionals being able to attend to more patients each day.
Learn More
What Are the HIPAA Secure Texting Rules?
The HIPAA secure texting rules mostly focus on protecting patient privacy; but also include other organizational procedural changes including when organizations and individuals should report suspected security breaches as well as conduct regular risk assessments on organizations and individuals.
Learn More
What Are Some Takeaways from Past HIPAA Audits and Text Messaging?
The HIPAA secure texting rules mostly focus on protecting patient privacy; but also include other organizational procedural changes including when organizations and individuals should report suspected security breaches as well as conduct regular risk assessments on organizations and individuals.
Learn More
What Are the HIPAA Compliant Texting Requirements?
HIPAA compliant texting requirements for HIPAA-compliant texting are categorized into three sections – physical safeguards, technical safeguards and administrative safeguards – and each of these safeguards must be fulfilled in order for the communication of ePHI to be HIPAA compliant over any electronic channel.
Learn More
What Are the HIPAA Laws and Texting Regulations?
The HIPAA laws and texting regulations focus primarily on protecting patient privacy, but also:
- Ban the selling or marketing of personal health information without obtaining prior permission from patients.
- Give patients the right to withhold details of any healthcare they have financed privately from the insurance company that covers their health insurance policy.
- Must tell patients within 60 days if a breach of personal health information is discovered which affects them.
- Require organizations to conduct periodic risk assessments to make sure that they comply with the HIPAA guidelines for texting.
- Require organizations and individuals with access to personal health information report when a suspected security breach is discovered.
Learn More
How is TigerConnect a HIPAA Secure Messaging Solution?
The secure text messaging application surpasses all the criteria for secure texting and HIPAA compliance and automatically generates read receipts to confirm a message has been read and eliminate the need for follow-up calls and phone tag. The application also produces access reports and audit logs in order that administrators can monitor use in compliance with the HIPAA secure messaging regulations.
Learn More